- MindByte Weekly Pulse: Weekly IT Insights: Quick GitHub, Azure, & .NET Updates
- Posts
- MindByte Issue #60: Navigating the New Digital Horizon
MindByte Issue #60: Navigating the New Digital Horizon
This week, we dive deep into GitHub's evolving landscape, from the Mercedes-Benz source code leak to cutting-edge GitHub Actions updates and .NET innovations. Discover how these developments are reshaping security, integration, and coding practices.
Welcome to issue #60 of MindByte, spotlighting the latest GitHub revelations and .NET advancements.
This edition delves into the challenges and innovations shaping our digital landscape, from security insights sparked by high-profile leaks to the newest features enhancing development workflows.
GitHub Digest
The Mercedes-Benz GitHub source code leak, stemming from a leaked employee token, exposes critical vulnerabilities in software supply chain security.
This incident highlights the dangers of sensitive data exposure due to human error and underscores the urgent need for robust security measures and awareness in handling access tokens and repositories. A deep dive into the cause and implications offers vital lessons for organizations aiming to fortify their defenses against similar breaches.
Harnessing the Power of Integration: EY's Strategic Move with GitHub and Azure DevOps
EY's strategic integration of GitHub with Microsoft Azure DevOps showcases an innovative approach to software development.
By migrating repositories to GitHub Enterprise and leveraging Azure DevOps for project management and CI/CD, EY has enhanced its security measures, accelerated development processes, and improved developer satisfaction.
Examples of their success include the acceptance of over 1.2 million lines of GitHub Copilot-created code and the deployment of GitHub Copilot and GitHub Codespaces to streamline developer workflows.
The Ripple Effect of Binance's GitHub Leak: A Financial Tsunami Warning
Binance's recent GitHub data leak, with passwords and site code exposed for months, has raised alarms over potential "severe financial harm."
This incident not only threatens the security integrity of Binance but also highlights the critical need for stringent data protection measures. The leaked data, including code related to passwords and multi-factor authentication, could provide hackers with a treasure trove for compromising Binance's systems.
This scenario underscores the ever-present risks in the digital finance world and the paramount importance of cybersecurity vigilance.
Elevating CI/CD Workflows: GitHub Actions Embraces macOS 14 Sonoma
GitHub has introduced macOS 14 (Sonoma) as the latest addition to its GitHub Actions runner images, providing a significant boost to CI/CD workflows.
This update, featuring the 3 vCPU M1 runner, enables developers to optimize their applications on the most current macOS environment, enhancing performance and security.
The transition to macOS 14 for 'latest' workflows is scheduled for Q2 FY24, highlighting GitHub's commitment to keeping its platform at the forefront of development innovation.
Streamlining Security and Compliance: Integrating Bicep Linting with GitHub Actions
Johnny Reilly's guide on integrating Bicep linting into Azure Pipelines and GitHub Actions showcases a seamless approach to improving code quality and adherence to best practices.
By leveraging the SARIF format, developers can easily incorporate the results of Bicep linting into GitHub's UI, making it straightforward to identify and address potential issues.
This method not only simplifies the process of maintaining high standards in infrastructure as code but also enhances security and compliance efforts with minimal effort.
Coding Corner
Fortifying GenAI in Azure: A Blueprint for Security Excellence
Microsoft's Azure blog outlines comprehensive security best practices for Generative AI applications, emphasizing the importance of safeguarding data, implementing Zero Trust principles, and ensuring privacy.
It highlights easy integration with SARIF to streamline lint results into GitHub, enhancing the security posture of AI-driven projects.
This guide serves as a critical resource for developers and administrators aiming to navigate the complexities of AI security with ease and efficiency.
Azure Updates & Insights
Cutting Costs, Not Corners: Azure's January 2024 Updates for Financial Management
The January 2024 updates from Microsoft Azure introduce several enhancements aimed at providing users with more control and better insights into their cloud spend.
Key highlights include improvements in cost management and billing, such as new cost analysis features for more granular tracking and optimization opportunities.
These updates are designed to help organizations manage their Azure expenses more effectively, ensuring they can maximize their cloud investment without compromising on performance or scalability.
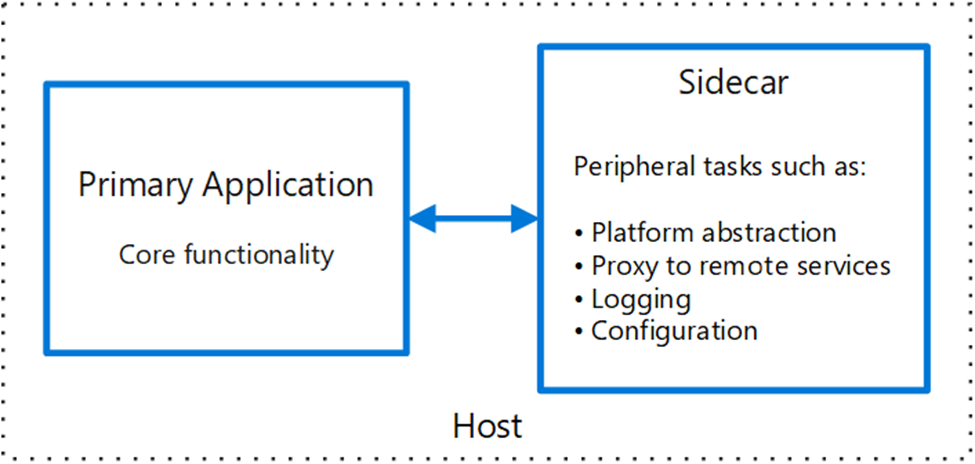
Revolutionizing App Architecture: The Sidecar Pattern on Linux App Service
Microsoft's recent blog post unveils the integration of the Sidecar pattern with Linux App Service, offering a glimpse into future application architecture enhancements.
This pattern facilitates the segregation of auxiliary services like logging, monitoring, and configuration from the main application, improving modularity and maintainability.
With practical examples and a step-by-step guide, the article illustrates the ease of deploying sidecar containers alongside main applications, promising significant benefits for cloud-native development.
.NET Nook
Expanding LINQ's Horizons: .NET 9 Introduces Three Game-Changing Methods
Steven Giesel's exploration of the alpha release of .NET 9 reveals the addition of three innovative LINQ methods: CountBy, AggregateBy, and Index.
These methods enhance data manipulation capabilities, offering more intuitive ways to group, aggregate, and index data collections.
Elevating Data Integrity in .NET 8: A Dive into New Data Annotations
Henrique Siebert Domareski unveils .NET 8's new DataAnnotations for advanced validation techniques, including string length, numeric range, and Base64 validations, through a detailed Web API project example.
This enhancement aids developers in maintaining robust data integrity with minimal effort.
Closing Thoughts
Thank you for joining me in this issue. I hope you found the insights shared both informative and thought-provoking.
Your feedback, article suggestions, or tips are always welcome—feel free to hit reply or subscribe if you haven't already.
Together, let's continue to explore the ever-evolving world of IT and development.





Join the conversation